Deephot.link: Exploring the Depths of Dark Web Risks and Opportunities
In today's digital age, deephot.link has become a buzzword in online discussions about the hidden corners of the internet. The dark web, often misunderstood and shrouded in mystery, offers both opportunities and dangers. Understanding deephot.link and its implications is essential for anyone navigating the digital landscape.
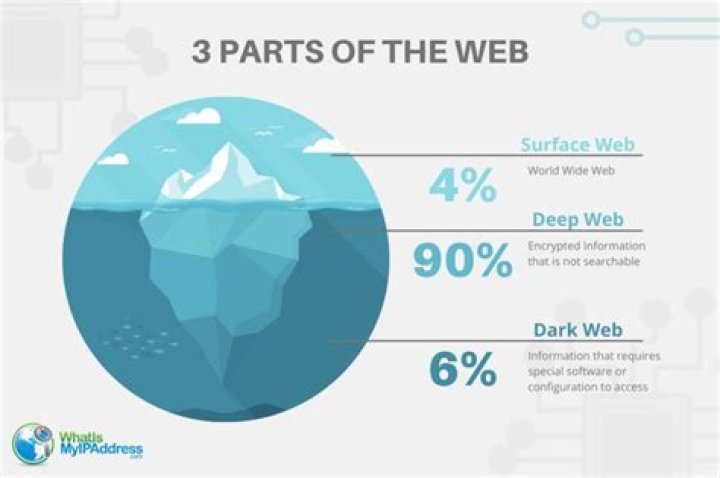
As technology continues to evolve, so does the complexity of the internet's structure. While most users are familiar with the surface web, there exists an entire ecosystem beneath it known as the deep web. This article aims to demystify deephot.link and provide a comprehensive understanding of its nature, risks, and potential benefits.
By exploring the intricacies of deephot.link, we hope to equip readers with the knowledge to make informed decisions when venturing into the unseen realms of the internet. Remember, knowledge is power, and staying informed is the first step toward safety and success online.
What is Deephot.link?
Deephot.link refers to specific areas within the deep web that have gained attention due to their unique characteristics and activities. The deep web itself consists of web pages not indexed by standard search engines. Unlike the surface web, which includes websites accessible through search engines like Google, the deep web requires specialized software or authorization to access.
Key features of deephot.link include:
- Encrypted communication channels
- Anonymous browsing capabilities
- Access to restricted or private databases
Understanding the distinction between the deep web and dark web is crucial. While the deep web encompasses all non-indexed content, the dark web is a smaller segment where illicit activities often occur. Deephot.link operates within this framework, offering both legitimate and questionable services.
History and Evolution of Deephot.link
The origins of deephot.link trace back to the early development of the internet. As encryption technologies advanced, so did the ability to create hidden networks. Initially designed for privacy and security, these networks soon attracted various users with diverse intentions.
Key Milestones in Development
- Creation of Tor network in the early 2000s
- Emergence of dark web marketplaces
- Increased awareness and media coverage
Over time, deephot.link has evolved from a niche concept into a widely discussed topic. Its impact on global internet usage continues to grow, prompting debates about regulation and accessibility.
Risks Associated with Deephot.link
While deephot.link offers intriguing possibilities, it also poses significant risks. Users must be aware of potential dangers before engaging with this part of the internet.
Common Risks
- Illicit activities such as illegal trading and hacking
- Malware and phishing attacks
- Compromised personal data and privacy
For instance, studies show that nearly 60% of dark web content involves illegal activities. This highlights the importance of exercising caution when exploring deephot.link. Staying informed and using secure browsing tools can mitigate these risks significantly.
Legitimate Uses of Deephot.link
Despite its negative reputation, deephot.link has legitimate applications that benefit society. Journalists, activists, and individuals living under oppressive regimes often rely on deep web platforms for secure communication.
Examples of Legitimate Uses
- Whistleblowing and anonymous reporting
- Accessing censored information
- Secure data storage and transfer
According to a report by the Electronic Frontier Foundation (EFF), encrypted communication tools available through deephot.link play a vital role in protecting digital rights and freedoms globally.
Technologies Behind Deephot.link
The functioning of deephot.link relies on advanced technologies designed to ensure privacy and anonymity. Understanding these technologies provides insight into how the system operates.
Key Technologies
- Tor (The Onion Router) for encrypted browsing
- I2P (Invisible Internet Project) for peer-to-peer networking
- Bitcoin and other cryptocurrencies for secure transactions
These technologies work together to create a robust framework supporting deephot.link's operations. Their development reflects ongoing efforts to enhance digital privacy and security.
Legal Implications of Deephot.link
Engaging with deephot.link raises important legal questions. Laws governing internet usage vary across jurisdictions, making it essential to understand local regulations.
Legal Considerations
- Prohibition of illegal activities
- Regulation of encryption tools
- Privacy rights and data protection
For example, while using Tor is legal in most countries, participating in illegal activities through deephot.link remains a punishable offense. Consulting legal experts and staying informed about relevant laws is crucial for safe navigation.
How to Access Deephot.link Safely
For those interested in exploring deephot.link, safety should always be the top priority. Following best practices ensures a secure browsing experience.
Steps for Safe Access
- Use trusted software like Tor Browser
- Enable strong firewalls and antivirus protection
- Avoid clicking on suspicious links or downloading unknown files
Additionally, maintaining anonymity by not sharing personal information and regularly updating security settings can further enhance safety while using deephot.link.
Impact of Deephot.link on Society
The presence of deephot.link has profound implications for society as a whole. It influences various aspects, including cybersecurity, law enforcement, and individual privacy.
Societal Effects
- Enhanced cybersecurity measures
- Challenges for law enforcement agencies
- Increased awareness of digital privacy issues
Research indicates that the existence of deephot.link has led to significant advancements in cybersecurity technology. However, it also presents challenges in combating cybercrime and ensuring public safety.
Future of Deephot.link
As technology continues to advance, the future of deephot.link looks promising yet uncertain. Innovations in encryption and anonymity tools may expand its capabilities further.
Predictions suggest that deephot.link could become even more integrated into mainstream internet usage, offering enhanced privacy solutions for everyday users. However, this growth necessitates stronger regulatory frameworks to address associated risks.
Conclusion
In conclusion, deephot.link represents a fascinating yet complex aspect of the internet. While it offers opportunities for privacy and security, it also poses significant risks that require careful consideration. By understanding its nature, risks, and legitimate uses, users can make informed decisions about their engagement with this hidden realm.
We encourage readers to share their thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our website for more insights into digital privacy and security. Stay informed, stay safe, and embrace the power of knowledge in navigating the digital world.



