IoT SSH Web Download Mac: The Ultimate Guide to Secure Connectivity
With the rapid advancement of technology, the Internet of Things (IoT) has become an integral part of modern living. IoT SSH web download Mac plays a crucial role in ensuring secure and seamless connectivity for devices operating on macOS systems. As more devices become interconnected, understanding how to securely manage these connections is vital for protecting sensitive data.
As the world becomes more connected, IoT devices continue to grow in number, and with them comes the need for secure access methods. Whether you're managing a smart home system or connecting to remote servers, utilizing SSH for IoT on macOS provides the necessary encryption and security protocols.
This article delves deep into IoT SSH web download Mac, exploring its applications, benefits, and best practices for implementation. Whether you're a tech enthusiast or a professional looking to enhance your network security, this guide is designed to provide comprehensive insights into the subject.
Introduction to IoT
The Internet of Things (IoT) refers to the network of physical devices embedded with sensors, software, and connectivity, enabling them to exchange data. This technology has transformed industries ranging from healthcare to manufacturing. Devices such as smart thermostats, wearable fitness trackers, and autonomous vehicles rely on IoT for functionality.
IoT devices require robust security measures to protect against unauthorized access and data breaches. One of the most reliable methods for securing IoT communication is through SSH (Secure Shell). By implementing SSH protocols, users can ensure encrypted data transmission between devices and servers.
In this section, we'll explore the basics of IoT and its growing significance in today's digital landscape. Understanding the fundamentals of IoT is essential for grasping the importance of secure connectivity solutions like IoT SSH web download Mac.
Understanding SSH
What is SSH?
SSH, or Secure Shell, is a cryptographic network protocol used to secure communication between devices over an unsecured network. It provides a secure channel for data exchange, ensuring confidentiality, integrity, and authentication. SSH is widely used for remote server management, file transfers, and secure command execution.
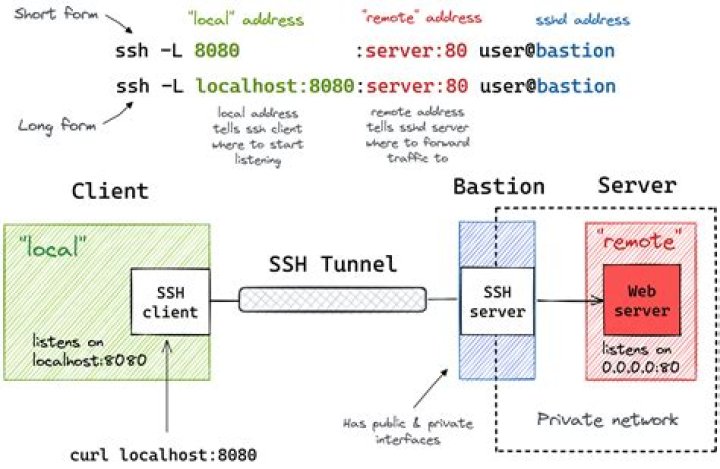
SSH operates on a client-server model, where the client initiates a connection to the server. During this process, encryption keys are exchanged to establish a secure session. This encryption ensures that even if data is intercepted, it remains unreadable to unauthorized parties.
How SSH Works
The SSH protocol uses a combination of symmetric and asymmetric encryption techniques to secure communication. Upon establishing a connection, SSH generates a unique session key that encrypts all subsequent data exchanges. This ensures that each session remains secure and independent of others.
In the context of IoT SSH web download Mac, SSH plays a critical role in securing communication between IoT devices and macOS systems. By leveraging SSH, users can remotely manage and monitor their IoT devices with confidence.
IoT SSH Web Download Mac Overview
IoT SSH web download Mac refers to the process of utilizing SSH protocols to securely connect IoT devices to macOS systems. This method allows users to manage and interact with their IoT devices from their Mac computers, ensuring data protection and streamlined operations.
By downloading and configuring SSH on macOS, users can establish secure tunnels for data transmission. This is particularly useful for managing IoT devices in remote locations or accessing sensitive information without compromising security.
Key features of IoT SSH web download Mac include:
- Encrypted communication channels
- Remote device management
- Secure file transfers
- Authentication and authorization protocols
Benefits of Using SSH for IoT
Enhanced Security
One of the primary advantages of using SSH for IoT is the enhanced security it provides. By encrypting all data transmissions, SSH ensures that sensitive information remains protected from unauthorized access. This is especially important for IoT devices handling personal or financial data.
Reliable Connectivity
SSH offers reliable connectivity even in challenging network conditions. Its robust protocols ensure stable connections, minimizing the risk of data loss or corruption during transmission.
Scalability
As IoT networks grow in size and complexity, SSH provides the scalability needed to manage multiple devices efficiently. Its ability to handle numerous connections simultaneously makes it an ideal choice for large-scale IoT deployments.
Setting Up SSH on Mac
Enabling SSH on macOS
To begin using SSH on your Mac, you'll first need to enable the SSH service. This can be done by navigating to System Preferences > Sharing and checking the box next to Remote Login. Once enabled, your Mac will be ready to accept SSH connections.
Configuring SSH Settings
After enabling SSH, you can configure its settings to suit your specific needs. This includes setting up authentication methods, such as public key or password-based authentication, and defining access permissions for authorized users.
Here are some steps to configure SSH on macOS:
- Open Terminal on your Mac
- Edit the SSH configuration file using a text editor
- Set desired parameters such as port numbers and encryption algorithms
- Save the changes and restart the SSH service
Security Best Practices
Use Strong Passwords
One of the simplest yet most effective ways to enhance SSH security is by using strong passwords. Avoid common phrases or easily guessable combinations, and consider implementing multi-factor authentication for added protection.
Implement Public Key Authentication
Public key authentication provides a more secure alternative to password-based authentication. By generating a pair of public and private keys, users can authenticate their identity without needing to enter a password each time.
Regularly Update Software
Keeping your SSH software up to date is crucial for maintaining security. Regular updates often include patches for known vulnerabilities, ensuring that your system remains protected against potential threats.
Troubleshooting Common Issues
While SSH is a reliable protocol, users may encounter issues during setup or operation. Some common problems include connection errors, authentication failures, and performance issues. Below are some troubleshooting tips to help resolve these challenges:
- Verify SSH service is enabled and running
- Check firewall settings to ensure SSH traffic is allowed
- Ensure correct port numbers and IP addresses are used
- Test connections using different clients or networks
Tools and Software
SSH Clients for Mac
Several SSH clients are available for macOS, offering various features and capabilities. Popular options include:
- Terminal: Built-in SSH client for Mac
- PuTTY: A widely used SSH client for Windows and Mac
- Cyberduck: A user-friendly FTP and SFTP client
SSH Servers for IoT Devices
When implementing SSH for IoT, selecting the right server software is essential. Some popular SSH servers for IoT devices include:
- OpenSSH: A widely adopted open-source SSH server
- Dropbear: A lightweight SSH server suitable for resource-constrained devices
- WolfSSH: A secure SSH library designed for embedded systems
Real-World Applications
IoT SSH web download Mac has numerous real-world applications across various industries. From smart homes to industrial automation, SSH provides the security and reliability needed for effective IoT deployments. Below are some examples of how SSH is used in practice:
- Remote monitoring of environmental sensors
- Secure management of industrial control systems
- Protected access to medical devices and healthcare records
Future of IoT and SSH
As IoT continues to evolve, the role of SSH in securing device communication will only grow in importance. Advances in encryption technologies and the development of quantum-resistant algorithms promise to enhance SSH's capabilities further. Additionally, the integration of AI and machine learning in IoT systems may lead to new security paradigms, with SSH playing a central role in this transformation.
Looking ahead, the future of IoT SSH web download Mac holds exciting possibilities for improving connectivity, security, and efficiency in interconnected systems.
Conclusion
In conclusion, IoT SSH web download Mac represents a powerful solution for securing IoT communications on macOS systems. By leveraging SSH protocols, users can ensure encrypted data transmission, reliable connectivity, and scalable management of IoT devices. This article has explored the fundamentals of IoT and SSH, outlined the benefits of using SSH for IoT, and provided practical guidance on setting up and securing SSH on Mac.
We encourage readers to take action by implementing the best practices discussed and exploring the tools and software available for enhancing their IoT security. Share your thoughts and experiences in the comments below, and don't forget to check out our other articles for more insights into the world of technology.
Sources: