Mastering IPTables PREROUTING: A Comprehensive Guide for Network Security
IPTables PREROUTING is a powerful feature in Linux that allows administrators to modify packets before they reach the destination application. This functionality plays a critical role in network security, load balancing, and traffic management. If you're exploring advanced networking configurations, understanding IPTables PREROUTING can elevate your skills and provide robust solutions for complex network challenges.
In today's digital landscape, where cyber threats are increasingly sophisticated, securing your network infrastructure is paramount. IPTables PREROUTING offers an effective way to filter, modify, and route incoming packets, ensuring that only authorized traffic enters your system. By mastering this feature, you can enhance your network's security posture and optimize resource utilization.
This article will take you through an in-depth exploration of IPTables PREROUTING, covering everything from basic concepts to advanced configurations. Whether you're a beginner or an experienced network administrator, this guide will equip you with the knowledge and tools needed to leverage IPTables PREROUTING effectively.
Introduction to IPTables PREROUTING
IPTables PREROUTING is one of the core chains in the Netfilter framework, which allows for packet manipulation before routing decisions are made. This chain is particularly useful for modifying packets that are destined for the local machine or routed through the system. By intercepting packets early in the network stack, administrators can implement advanced rules for packet filtering, address translation, and more.
In the context of network security, IPTables PREROUTING provides a critical layer of protection by enabling administrators to enforce strict access controls and filter out malicious traffic. This functionality is especially valuable in environments where external threats are prevalent, such as public-facing servers or cloud-based infrastructures.
Understanding the PREROUTING chain requires familiarity with the overall IPTables framework and its associated components. This section will provide a foundational overview of IPTables and how the PREROUTING chain fits into the larger picture of network management.
IPTables Overview
What is IPTables?
IPTables is a user-space utility program that allows system administrators to configure the tables provided by the Linux kernel's netfilter framework. These tables consist of chains, which are lists of rules that define how packets should be processed. IPTables operates on the principle of packet filtering, enabling administrators to control network traffic based on specific criteria.
Key Components of IPTables
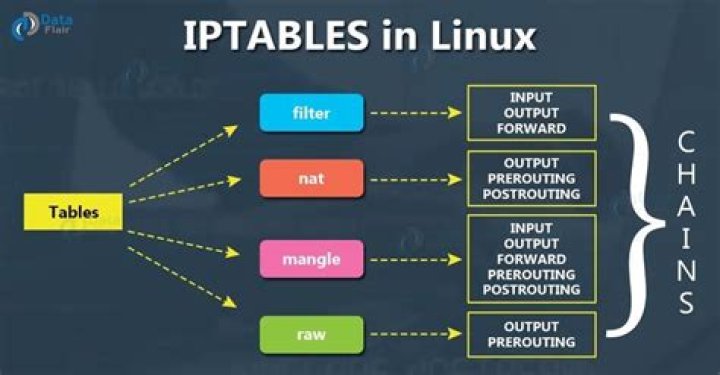
- Tables: IPTables consists of multiple tables, each serving a specific purpose. The most commonly used tables include filter, nat, mangle, and raw.
- Chains: Chains are sequences of rules within a table. Common chains include INPUT, OUTPUT, FORWARD, PREROUTING, and POSTROUTING.
- Rules: Rules define the actions to be taken on packets that match specific criteria. These actions can include accepting, dropping, rejecting, or modifying packets.
Why Use IPTables?
IPTables offers unparalleled flexibility and control over network traffic, making it an essential tool for administrators seeking to secure their systems. Its ability to integrate seamlessly with the Linux kernel ensures high performance and reliability, making it a popular choice for both small-scale and enterprise-level deployments.
Understanding the PREROUTING Chain
The PREROUTING chain is part of the nat table in IPTables and is responsible for processing packets immediately after they enter the system but before any routing decisions are made. This chain is particularly useful for tasks such as Network Address Translation (NAT), port forwarding, and traffic redirection.
When a packet enters the system, it first passes through the PREROUTING chain, where it can be modified according to predefined rules. These modifications can include changing the source or destination IP address, altering port numbers, or redirecting traffic to different services.
Understanding the flow of packets through the PREROUTING chain is crucial for designing effective firewall rules and optimizing network performance. By leveraging this chain, administrators can implement advanced configurations that enhance both security and functionality.
Key Use Cases of IPTables PREROUTING
Port Forwarding
One of the most common use cases for IPTables PREROUTING is port forwarding. This technique allows administrators to redirect incoming traffic from one port to another, enabling services to run on non-standard ports while maintaining accessibility.
Network Address Translation (NAT)
IPTables PREROUTING is essential for implementing NAT, which involves modifying the source or destination IP addresses of packets. This functionality is particularly useful in scenarios where multiple devices share a single public IP address.
Traffic Redirection
By using PREROUTING rules, administrators can redirect traffic to specific services or applications based on predefined criteria. This capability is invaluable for load balancing, content filtering, and implementing custom network policies.
Configuring IPTables PREROUTING
Configuring IPTables PREROUTING involves defining rules that specify how packets should be processed. Below are some examples of common configurations:
Basic Port Forwarding
To forward incoming traffic on port 80 to port 8080, you can use the following command:
iptables -t nat -A PREROUTING -p tcp --dport 80 -j REDIRECT --to-port 8080
Network Address Translation
For NAT, you can modify the destination IP address of packets using the DNAT target:
iptables -t nat -A PREROUTING -d ORIGINAL_IP -p tcp --dport 22 -j DNAT --to-destination NEW_IP
Traffic Redirection
To redirect traffic destined for a specific IP address to a different service, use the following rule:
iptables -t nat -A PREROUTING -d TARGET_IP -p tcp --dport 443 -j DNAT --to-destination SERVICE_IP:443
Advanced Techniques for PREROUTING
While basic configurations provide foundational functionality, advanced techniques can unlock the full potential of IPTables PREROUTING. Below are some examples:
Load Balancing
By implementing PREROUTING rules with load balancing algorithms, administrators can distribute incoming traffic across multiple servers, ensuring optimal performance and reliability.
Content Filtering
Using PREROUTING, administrators can filter incoming traffic based on specific criteria, such as IP addresses, protocols, or content types. This capability is particularly useful for implementing security policies and blocking malicious traffic.
Custom Network Policies
With IPTables PREROUTING, administrators can define custom network policies that cater to specific organizational requirements. These policies can include traffic shaping, quality of service (QoS) configurations, and more.
Troubleshooting Common Issues
When working with IPTables PREROUTING, administrators may encounter various issues. Below are some common problems and their solutions:
Rules Not Applying
If PREROUTING rules are not being applied, ensure that the correct table and chain are being used. Additionally, verify that the rules are in the correct order and that no conflicting rules exist.
Performance Degradation
Complex PREROUTING configurations can lead to performance degradation. To mitigate this, optimize rules by removing unnecessary entries and using efficient matching criteria.
Unexpected Behavior
In cases of unexpected behavior, review the complete IPTables configuration to identify potential conflicts or misconfigurations. Using tools like iptables-save can help in diagnosing issues.
Optimizing IPTables PREROUTING Performance
Optimizing IPTables PREROUTING involves streamlining rules, reducing overhead, and ensuring efficient processing. Below are some strategies for achieving optimal performance:
Rule Simplification
Simplify rules by combining similar entries and eliminating redundant configurations. This approach reduces the processing overhead and improves overall performance.
Rule Ordering
Place frequently used rules at the top of the chain to minimize the number of comparisons required for packet processing. This technique can significantly enhance performance, especially in high-traffic environments.
Using Efficient Matching Criteria
Use specific and efficient matching criteria to ensure that rules are applied only to relevant packets. This approach minimizes unnecessary processing and improves system efficiency.
Security Best Practices
Implementing IPTables PREROUTING requires adherence to security best practices to ensure the integrity and confidentiality of network traffic. Below are some recommendations:
Regular Audits
Conduct regular audits of IPTables configurations to identify and address potential vulnerabilities. This practice ensures that security policies remain up-to-date and effective.
Least Privilege Principle
Apply the least privilege principle by granting only the necessary permissions for each rule. This approach minimizes the attack surface and reduces the risk of unauthorized access.
Monitoring and Logging
Enable monitoring and logging for IPTables PREROUTING to detect and respond to suspicious activities promptly. Analyzing logs can provide valuable insights into network behavior and help identify potential threats.
Conclusion and Next Steps
In conclusion, IPTables PREROUTING is a powerful tool that offers administrators unparalleled control over network traffic. By understanding its functionality and implementing effective configurations, you can enhance your network's security and performance. Whether you're implementing basic port forwarding or advanced load balancing techniques, IPTables PREROUTING provides the flexibility and scalability needed for modern network environments.
We encourage readers to explore the concepts discussed in this article and experiment with IPTables PREROUTING in their own environments. For further learning, consider reading additional resources on IPTables and network security. Don't forget to share your thoughts and experiences in the comments section below!



