Remote Connect IoT Behind Firewall on Mac: Comprehensive Guide Without Windows
In today's interconnected world, remote connectivity for IoT devices has become a necessity. Whether you're managing smart home systems, industrial sensors, or enterprise devices, the ability to connect remotely behind a firewall is crucial. However, achieving this on a Mac without relying on Windows can be challenging. This article will guide you step-by-step through the process, ensuring secure and efficient remote access.
Connecting IoT devices remotely behind a firewall is no longer just a technical challenge—it's a requirement for modern businesses and individuals. As the Internet of Things continues to grow, so does the need for secure and reliable access to these devices. This guide will provide you with practical solutions and insights to achieve this seamlessly on a Mac.
By the end of this article, you will understand the fundamentals of remote IoT connectivity, the role of firewalls, and how to set up a secure connection without using Windows. Let's dive in!
Introduction
Remote connectivity for IoT devices has revolutionized the way we interact with technology. Whether you're a developer, IT professional, or simply someone who manages IoT devices, understanding how to connect remotely behind a firewall is essential. This article focuses on remote connect IoT behind firewall mac download without windows, providing a comprehensive guide to help you achieve secure and efficient access.
The increasing reliance on IoT devices means that traditional methods of connectivity are no longer sufficient. Firewalls, while crucial for security, can pose challenges when trying to access devices remotely. This guide will walk you through the necessary steps to overcome these challenges on a Mac, ensuring that your devices remain accessible and secure.
Understanding IoT and Firewalls
What is IoT?
The Internet of Things (IoT) refers to the network of physical devices embedded with sensors, software, and connectivity, enabling them to exchange data. These devices range from smart home appliances to industrial machinery, all designed to enhance efficiency and automation.
Role of Firewalls in IoT
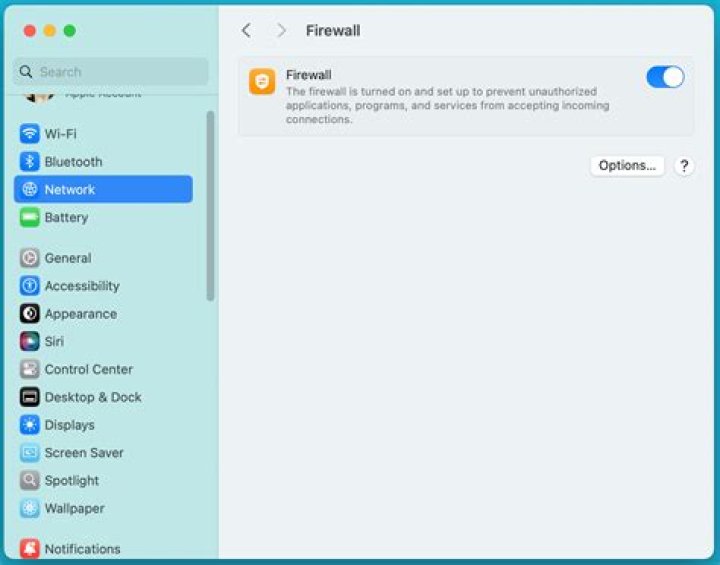
Firewalls play a critical role in securing IoT devices by filtering incoming and outgoing network traffic. They act as a barrier between your devices and potential threats, ensuring that only authorized connections are allowed. However, this security measure can sometimes hinder remote access, making it necessary to configure firewalls properly.
Challenges of Remote Connectivity
Connecting IoT devices remotely behind a firewall presents several challenges. These include:
- Network Restrictions: Firewalls often block unauthorized access, making it difficult to establish a connection.
- Security Concerns: Ensuring that remote access does not compromise device security is paramount.
- Compatibility Issues: Different devices and operating systems may require unique configurations.
Mac-Specific Solutions for Remote IoT Connectivity
Using SSH for Secure Connections
SSH (Secure Shell) is a protocol that provides secure communication over an unsecured network. On a Mac, you can use SSH to connect to IoT devices behind a firewall. Here's how:
- Install an SSH client on your Mac.
- Configure the firewall to allow SSH traffic.
- Establish a connection using the device's IP address and credentials.
Port Forwarding Techniques
Port forwarding allows you to redirect incoming traffic from one port to another, enabling remote access to devices behind a firewall. To implement this on a Mac:
- Access your router's settings.
- Set up port forwarding rules for the desired ports.
- Test the connection to ensure it works.
Essential Tools and Software
Software Recommendations
Several tools and software can facilitate remote IoT connectivity on a Mac. Some popular options include:
- TunnelBear: A user-friendly VPN service that simplifies remote access.
- ngrok: A tool that creates secure tunnels to localhost, enabling remote access without complex configurations.
- TeamViewer: A versatile remote access solution that works seamlessly on Mac.
Downloading Necessary Software
When downloading software for remote IoT connectivity, ensure that you obtain it from trusted sources. Websites like the official repositories or reputable developers' websites are ideal. Always verify the integrity of the software before installation.
Security Best Practices
Encrypting Data Transfers
Encrypting data transfers is crucial for maintaining security during remote IoT connections. Use protocols like SSL/TLS to ensure that all data exchanged between devices is encrypted and protected from unauthorized access.
Regular Updates and Patches
Keeping your software and firmware up to date is essential for addressing security vulnerabilities. Regularly check for updates and apply patches as soon as they become available.
Implementing Two-Factor Authentication
Two-factor authentication (2FA) adds an extra layer of security to your remote IoT connections. By requiring a second form of verification, such as a one-time code, you can significantly reduce the risk of unauthorized access.
Troubleshooting Common Issues
Connection Failures
If you encounter connection failures, consider the following steps:
- Check your firewall settings to ensure that the necessary ports are open.
- Verify the IP address and credentials of the IoT device.
- Restart your router and try reconnecting.
Performance Issues
Slow or inconsistent performance can be frustrating when managing IoT devices remotely. To address this:
- Optimize your network settings for better performance.
- Monitor bandwidth usage and adjust as needed.
- Consider upgrading your hardware if necessary.
Case Studies: Real-World Examples
Case Study 1: Smart Home Automation
A homeowner wanted to remotely manage their smart home devices from their Mac. By implementing SSH and port forwarding, they were able to securely access and control their devices, enhancing convenience and security.
Case Study 2: Industrial IoT Monitoring
An industrial facility needed to monitor IoT sensors remotely. Using a combination of ngrok and SSL encryption, they established a secure connection that allowed real-time monitoring and data analysis.
Comparison with Windows-Based Solutions
Key Differences
While both Mac and Windows offer solutions for remote IoT connectivity, there are some key differences:
- User Interface: Mac provides a more streamlined and intuitive interface for many users.
- Software Availability: Some tools may be more readily available on Windows, but Mac has its own robust offerings.
- Security Features: Both platforms have strong security features, but Mac's focus on simplicity can be advantageous.
Future Trends in IoT Remote Connectivity
Advancements in Security
As IoT continues to evolve, so do the security measures surrounding remote connectivity. Expect to see advancements in encryption, authentication, and network security protocols, making it easier and safer to connect devices remotely.
Increased Automation
Automation will play a significant role in the future of IoT remote connectivity. With the development of AI-driven solutions, managing devices remotely will become more efficient and less reliant on manual intervention.
Conclusion
Remote connect IoT behind firewall mac download without windows is an achievable goal with the right tools and knowledge. By understanding the fundamentals of IoT, firewalls, and remote connectivity, you can establish secure and efficient connections to your devices. Remember to follow security best practices and stay updated with the latest trends to ensure optimal performance.
We encourage you to share your experiences and insights in the comments section below. Additionally, feel free to explore other articles on our site for more information on IoT and related technologies. Together, let's continue to advance the field of remote connectivity and secure IoT management.



