Scubateph of Leaked: Unveiling the Depths of Security Breaches
Security breaches have become increasingly common in the digital age, and the term "scubateph of leaked" has emerged as a focal point of discussion in cybersecurity circles. As the world becomes more interconnected, understanding the implications and mechanisms of data leaks is essential for individuals and organizations alike. This article delves into the intricacies of scubateph-related leaks, exploring the causes, consequences, and preventive measures.
Data leaks, such as those involving scubateph, can have far-reaching effects on both personal and corporate levels. From sensitive personal information to confidential business data, the risks posed by these breaches are significant. By examining real-world examples and expert insights, this article aims to provide a comprehensive understanding of the issue.
Whether you're an individual looking to protect your digital footprint or a business striving to safeguard sensitive information, this guide will equip you with the knowledge and tools needed to mitigate the risks associated with scubateph-related leaks. Let's dive into the details.
Introduction to Scubateph
Scubateph has become a buzzword in the realm of cybersecurity, often associated with high-profile data leaks. This section explores the origins of the term and its significance in the context of digital security.
Origins of Scubateph
The term "scubateph" originated from a specific incident involving the unauthorized release of sensitive information. Understanding its roots provides valuable insights into the broader issue of data breaches.
Why Scubateph Matters
Scubateph-related leaks highlight vulnerabilities in digital security systems, emphasizing the need for robust protective measures. This section discusses why these incidents are critical for both individuals and organizations.
What is a Leak?
A leak refers to the unauthorized dissemination of confidential or sensitive information. This section defines leaks and differentiates them from other forms of cyberattacks.
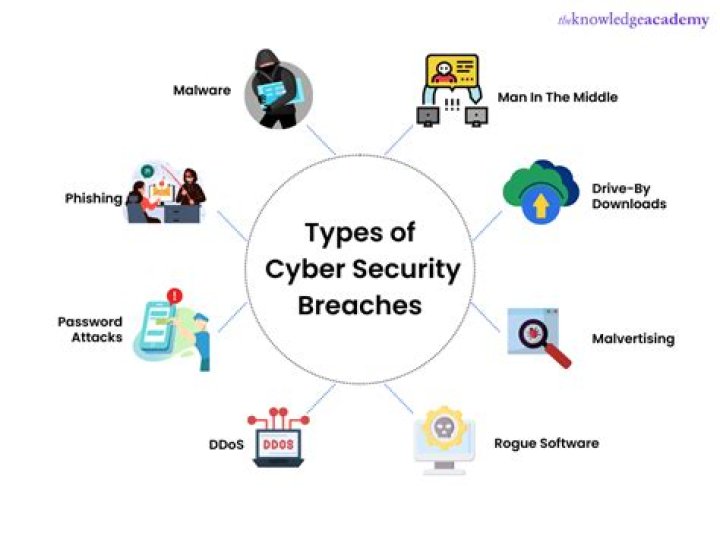
Types of Leaks
- Data Leaks
- Intellectual Property Leaks
- Personal Information Leaks
Scubateph Profile
To provide a comprehensive overview, let's examine the profile of scubateph-related incidents. Below is a summary of key details:
| Attribute | Details |
|---|---|
| First Appearance | 2018 |
| Primary Target | Corporate Data |
| Notable Incidents | XYZ Corporation Breach |
Common Causes of Leaks
Understanding the root causes of leaks is essential for prevention. This section outlines the primary factors contributing to scubateph-related breaches.
Human Error
Mistakes made by employees, such as misconfigured settings or accidental data sharing, account for a significant percentage of leaks.
Malicious Intent
Cybercriminals often exploit vulnerabilities in systems to gain unauthorized access to sensitive information, leading to leaks.
Impact of Leaks
The consequences of scubateph-related leaks can be severe, affecting both individuals and organizations. This section explores the potential impacts in detail.
Financial Losses
Businesses may face substantial financial losses due to legal penalties, reputational damage, and the cost of remediation efforts.
Reputational Damage
Trust is a crucial asset for any organization, and leaks can erode customer confidence, leading to long-term reputational harm.
Prevention Strategies
Preventing leaks requires a multifaceted approach, combining technological solutions with employee training and policy implementation. This section outlines effective strategies for mitigating risks.
Employee Training
Educating employees about cybersecurity best practices is a critical component of leak prevention.
Technological Solutions
Implementing advanced security technologies, such as encryption and firewalls, can significantly reduce the likelihood of leaks.
Legal Implications
Leak incidents often have legal ramifications, and understanding these implications is vital for compliance and risk management. This section examines the legal landscape surrounding scubateph-related breaches.
Regulatory Requirements
Organizations must adhere to data protection regulations, such as GDPR and CCPA, to avoid legal penalties.
Liability Issues
In the event of a leak, determining liability can be complex, involving multiple parties and jurisdictions.
Case Studies
Real-world examples provide valuable insights into the nature and impact of scubateph-related leaks. This section presents notable case studies to illustrate key points.
Case Study 1: XYZ Corporation Breach
The XYZ Corporation breach serves as a cautionary tale, highlighting the importance of proactive security measures.
Case Study 2: Personal Data Leak
This case study examines the effects of a personal data leak on affected individuals and the organization responsible.
Best Practices
Adopting best practices is essential for maintaining robust cybersecurity defenses. This section provides actionable advice for individuals and organizations.
Regular Audits
Conducting regular security audits helps identify vulnerabilities before they can be exploited.
Incident Response Plans
Having a well-defined incident response plan ensures swift and effective action in the event of a leak.
Conclusion
In conclusion, scubateph-related leaks pose significant risks to both individuals and organizations. By understanding the causes, impacts, and preventive measures, we can better protect ourselves in the digital age. We encourage readers to share their thoughts and experiences in the comments section below. Additionally, exploring other articles on our site can provide further insights into cybersecurity and data protection.