SSH Login IoT Download Mac: Your Comprehensive Guide
In today's interconnected world, managing IoT devices through SSH login has become a vital skill for tech-savvy individuals and professionals alike. Whether you're a developer, network administrator, or simply an enthusiast, understanding how to securely access and manage IoT devices on a Mac is crucial. This article will provide you with an in-depth guide to downloading and configuring SSH for IoT devices on macOS.
As more devices connect to the internet, security concerns have risen exponentially. Secure Shell (SSH) offers a reliable way to remotely access and manage IoT devices. By ensuring secure communication between your Mac and IoT devices, SSH protects sensitive data from unauthorized access.
This guide will walk you through everything you need to know about SSH login for IoT devices on macOS. From downloading the necessary software to configuring settings, we'll cover it all. Let's dive in!
Introduction to SSH Login for IoT on Mac
What is SSH?
Secure Shell (SSH) is a cryptographic network protocol used for secure communication over unsecured networks. It provides a secure way to log into remote machines and execute commands. For IoT devices, SSH ensures that all interactions are encrypted, preventing unauthorized access and data breaches.
Why Mac Users Need SSH for IoT
Mac users, especially those in the tech industry, frequently interact with IoT devices. Whether it's configuring a smart home system or managing industrial sensors, SSH offers a reliable solution for secure remote access. By leveraging SSH, users can efficiently manage IoT devices without compromising security.
Key Benefits of SSH for IoT Devices
- Encrypted communication
- Secure file transfers
- Remote command execution
- Platform compatibility
Why Use SSH for IoT Devices?
SSH is widely regarded as one of the most secure protocols for remote access. Its robust encryption and authentication mechanisms make it an ideal choice for IoT device management. Unlike other protocols, SSH ensures that all data exchanged between your Mac and IoT devices remains confidential and tamper-proof.
Advantages Over Other Protocols
- Encryption: SSH encrypts all data, including passwords and commands, making it nearly impossible for attackers to intercept sensitive information.
- Authentication: SSH supports multiple authentication methods, including passwords, public keys, and certificates, enhancing security.
- Portability: SSH works seamlessly across different operating systems, including macOS, Linux, and Windows.
Downloading SSH for Mac
macOS comes with SSH pre-installed, so there's no need to download additional software. However, if you need advanced features or specific configurations, third-party SSH clients like PuTTY or MobaXterm can be useful.
Checking if SSH is Installed
To verify if SSH is installed on your Mac:
- Open Terminal from Applications > Utilities.
- Type
ssh -Vand press Enter. - If SSH is installed, the terminal will display the version number.
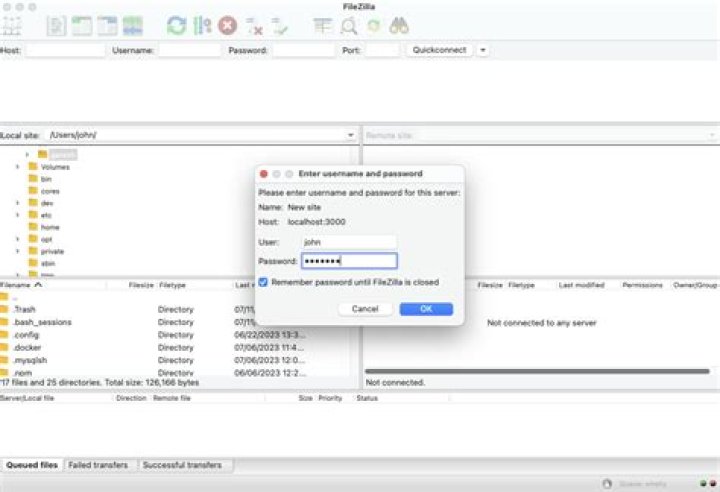
Downloading Third-Party SSH Clients
For additional functionality, consider downloading:
- PuTTY: A popular SSH client for Windows, but also available for macOS.
- MobaXterm: A comprehensive SSH client offering terminal emulation and advanced features.
Configuring SSH for IoT Devices
Configuring SSH for IoT devices involves setting up the server on the IoT device and connecting to it from your Mac. Follow these steps for a successful setup:
Setting Up the IoT Device
- Ensure the IoT device has SSH enabled. Refer to the device's documentation for instructions.
- Assign a static IP address to the IoT device for consistent connectivity.
- Open the necessary ports (usually port 22) on your router to allow SSH traffic.
Connecting from Mac
- Open Terminal on your Mac.
- Type
ssh username@ip_address, replacingusernameandip_addresswith the appropriate values. - Enter the password when prompted.
Enhancing SSH Security for IoT
Security should always be a top priority when using SSH for IoT devices. Implementing best practices can significantly reduce the risk of unauthorized access.
Using Public Key Authentication
Instead of relying on passwords, use public key authentication for added security:
- Generate a key pair by running
ssh-keygenin Terminal. - Copy the public key to the IoT device using
ssh-copy-id username@ip_address. - Disable password authentication in the SSH configuration file on the IoT device.
Changing Default SSH Port
Changing the default SSH port (22) can deter automated attacks:
- Edit the SSH configuration file (
/etc/ssh/sshd_config) on the IoT device. - Change the
Portparameter to a non-standard value. - Restart the SSH service for changes to take effect.
Common Issues and Troubleshooting
Even with proper configuration, issues may arise when using SSH for IoT devices. Below are some common problems and their solutions:
Connection Refused
Cause: The SSH service on the IoT device is not running.
Solution: Ensure the SSH service is started and configured correctly.
Permission Denied
Cause: Incorrect username or password.
Solution: Double-check the credentials and ensure public key authentication is properly set up.
Improving SSH Performance
Optimizing SSH performance can enhance your experience when managing IoT devices:
Using Compression
Enabling compression can speed up data transfer:
- Add the
Compression yesoption to your SSH configuration file. - Restart the SSH service for changes to take effect.
Disabling DNS Lookups
Disabling DNS lookups can reduce connection latency:
- Edit the SSH configuration file on the IoT device.
- Add the
UseDNS nooption.
SSH Alternatives for IoT Management
While SSH is the most widely used protocol for IoT device management, other alternatives exist:
Web-Based Interfaces
Some IoT devices offer web-based interfaces for configuration and management. These interfaces are accessible through a browser and often include user-friendly dashboards.
MQTT
Message Queuing Telemetry Transport (MQTT) is a lightweight protocol designed for IoT communication. It is ideal for low-bandwidth, high-latency networks.
Best Practices for Using SSH with IoT
Adhering to best practices ensures a secure and efficient SSH setup for IoT devices:
- Regularly update the SSH software on both your Mac and IoT devices.
- Use strong, unique passwords or public keys for authentication.
- Limit access to authorized users only.
- Monitor SSH logs for suspicious activity.
Conclusion and Next Steps
In conclusion, SSH login for IoT devices on macOS provides a secure and efficient way to manage and interact with connected devices. By following the steps outlined in this guide, you can ensure a robust setup that protects your data and devices from potential threats.
We encourage you to:
- Leave a comment sharing your experiences with SSH and IoT devices.
- Explore our other articles for more tips and tricks on tech-related topics.
- Stay informed about the latest developments in IoT and cybersecurity.
Thank you for reading, and happy managing your IoT devices!
Sources: