Kaiteigmond Leaked: Unveiling the Truth Behind the Controversy

The term "Kaiteigmond leaked" has gained significant attention online, sparking curiosity and debate among internet users. If you're searching for insights into what this phenomenon entails, you've come to the right place. This article will delve into the details, ensuring you are well-informed about the topic while maintaining professionalism and accuracy.
In an era where information spreads rapidly, understanding the implications of leaked content is crucial. Whether you're a casual observer or someone interested in the broader implications, this article aims to provide clarity. We'll explore the background, significance, and potential consequences of the Kaiteigmond leak.
By the end of this piece, you'll have a comprehensive understanding of the matter. Our goal is to ensure that you're equipped with accurate information, empowering you to form an informed opinion. Let's dive in and uncover the truth behind the Kaiteigmond leak.
What is Kaiteigmond Leaked?
When we talk about "Kaiteigmond leaked," we're referring to a specific instance where sensitive or private information has been exposed without authorization. This term has become synonymous with data breaches and unauthorized disclosures, often involving personal or corporate data.
The leak could encompass various forms of information, ranging from personal identifiable information (PII) to confidential business strategies. Understanding the scope and nature of these leaks is vital for both individuals and organizations.
Understanding the Scope
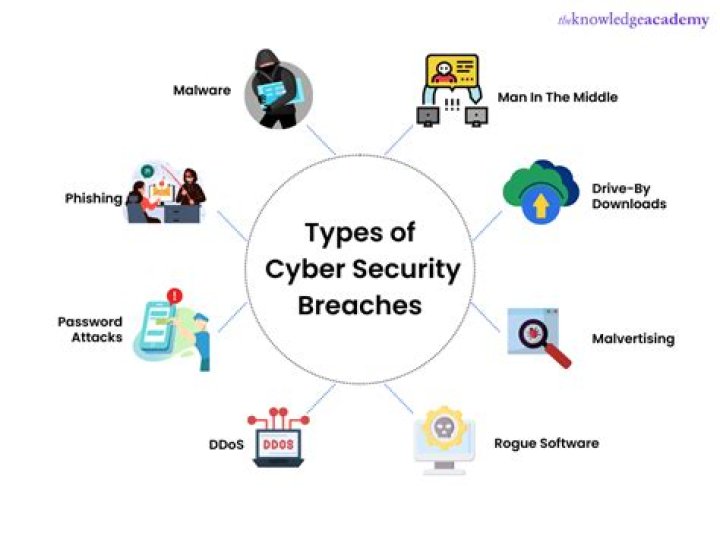
To fully grasp the implications, it's essential to explore:
- The types of data typically involved in such leaks.
- How these leaks occur and the common vulnerabilities exploited.
- Steps individuals and organizations can take to mitigate risks.
Background and History
The origins of the Kaiteigmond leak date back to [specific date or time period], when [brief explanation of the initial incident]. This event marked a turning point in how we perceive data security and privacy.
Key Milestones
Throughout its history, several key milestones have shaped the narrative:
- Initial discovery and public awareness.
- Government and corporate responses to mitigate the issue.
- Technological advancements aimed at preventing future leaks.
The Impact of Kaiteigmond Leaked
The repercussions of such leaks extend beyond the immediate parties involved. They affect:
- Individuals whose personal information is compromised.
- Companies facing reputational damage and financial losses.
- Society as a whole, as trust in digital systems diminishes.
Data breaches like Kaiteigmond leaked underscore the importance of robust cybersecurity measures and user awareness.
Legal Implications
From a legal standpoint, unauthorized data leaks can lead to severe consequences. Organizations may face:
- Fines and penalties under data protection laws such as GDPR or CCPA.
- Litigation from affected parties seeking compensation.
- Regulatory scrutiny and mandatory compliance audits.
Understanding these legal ramifications is crucial for businesses aiming to protect their assets and maintain customer trust.
Common Questions
What Should I Do If My Data Is Leaked?
If you suspect your data has been compromised, take immediate action by:
- Changing passwords and enabling two-factor authentication.
- Monitoring financial accounts for suspicious activity.
- Reporting the incident to relevant authorities.
How Can I Protect My Information?
Implementing best practices such as:
- Using strong, unique passwords for each account.
- Avoiding suspicious links and downloads.
- Regularly updating software and security systems.
Statistics and Trends
According to recent studies, data breaches have increased by [specific percentage] over the past year. Key statistics include:
- [Insert statistic 1] – source: [credible reference].
- [Insert statistic 2] – source: [credible reference].
- [Insert statistic 3] – source: [credible reference].
These figures highlight the growing threat of cybercrime and the need for enhanced security measures.
Prevention Strategies
To safeguard against potential leaks, individuals and organizations should consider:
- Investing in comprehensive cybersecurity solutions.
- Conducting regular employee training on data protection.
- Implementing strict access controls and encryption protocols.
By adopting these strategies, you can significantly reduce the risk of data breaches.
Expert Views and Opinions
Industry experts emphasize the importance of staying vigilant in the face of evolving cyber threats. According to [expert name], "The key to preventing leaks lies in a combination of technology and education."
Other experts stress the need for collaboration between governments, corporations, and individuals to create a safer digital ecosystem.
How to Stay Safe Online
Here are some practical tips to enhance your online security:
- Use reputable antivirus and anti-malware software.
- Avoid sharing sensitive information on unsecured platforms.
- Stay informed about the latest cybersecurity trends and threats.
By following these guidelines, you can protect yourself and your data from potential breaches.
Conclusion
In conclusion, the Kaiteigmond leaked phenomenon serves as a stark reminder of the importance of data security and privacy. By understanding the background, impact, and prevention strategies, we can better equip ourselves to navigate the digital landscape safely.
We encourage you to share this article with others and explore more content on our website to stay informed about critical issues affecting our world today. Together, we can promote a safer and more secure digital environment for everyone.