Lexi 2 Legit Leaked: The Facts You Need to Know

In today's digital age, the term "Lexi 2 Legit Leaked" has sparked significant interest and debate across various online platforms. Whether you're a tech enthusiast, a content creator, or simply someone curious about digital privacy, understanding this phenomenon is crucial. Lexi 2 Legit Leaked refers to the unauthorized release of content or data that was originally intended for a specific audience. This breach not only raises questions about digital security but also highlights the importance of safeguarding personal information.
The impact of such leaks can be far-reaching, affecting both individuals and organizations. It is essential to delve deeper into what exactly Lexi 2 Legit Leaked entails, its implications, and how one can protect themselves in an increasingly interconnected world. In this article, we will explore the topic comprehensively, ensuring that you are well-informed about the matter.
As we navigate through this article, we will also discuss the legal and ethical considerations surrounding leaks like Lexi 2 Legit. By the end of this piece, you will have a clearer understanding of the situation and be equipped with actionable insights to safeguard your digital presence.
Introduction to Lexi 2
Lexi 2 is a term often associated with digital content, software, or data that has gained significant attention in recent years. It represents a specific type of digital asset that has been the subject of scrutiny due to unauthorized access or distribution. Understanding Lexi 2 requires an exploration of its origins, purpose, and the context in which it operates.
Initially, Lexi 2 was designed to serve a particular function, often within a closed or controlled environment. However, the emergence of leaks like Lexi 2 Legit Leaked has raised concerns about the security measures in place to protect such digital assets. This section will provide an overview of Lexi 2, its intended use, and the potential risks associated with its unauthorized release.
Origins and Development
The development of Lexi 2 can be traced back to advancements in technology and the growing demand for digital solutions. As more businesses and individuals rely on digital platforms, the need for robust security measures becomes increasingly apparent. However, the complexity of digital systems can sometimes lead to vulnerabilities that are exploited by malicious actors.
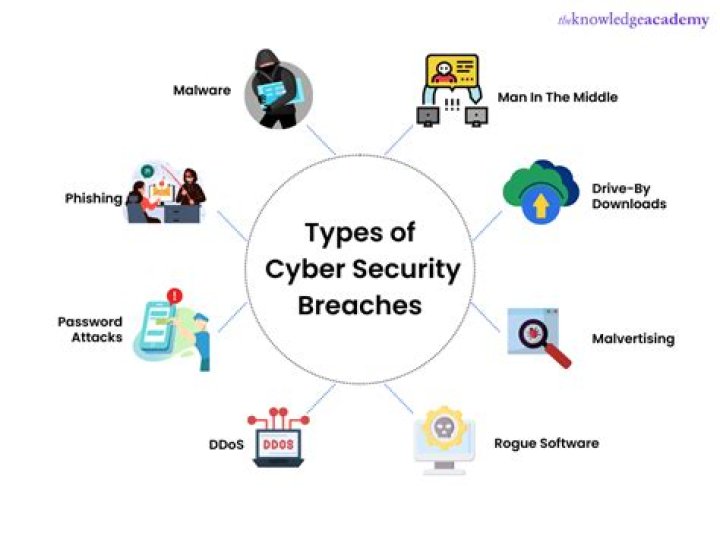
What is a Leak?
A leak, in the context of digital security, refers to the unauthorized release of information, content, or data that was originally intended to remain private or restricted. Leaks can occur in various forms, including data breaches, insider threats, or hacking incidents. The consequences of such leaks can be severe, affecting both individuals and organizations alike.
Types of Leaks
- Data Breaches: Occur when sensitive information is accessed without authorization.
- Insider Threats: Involve individuals within an organization who intentionally or unintentionally disclose confidential data.
- Hacking Incidents: Result from cyberattacks aimed at gaining unauthorized access to systems or networks.
Lexi 2 Legit Leaked: Details
The specifics surrounding Lexi 2 Legit Leaked have been a subject of intense discussion. Reports indicate that the leak involved sensitive content or data that was not meant for public consumption. Understanding the details of this incident is crucial in addressing the underlying security issues and preventing similar occurrences in the future.
Scope and Impact
The scope of the Lexi 2 Legit Leaked incident extends beyond the immediate parties involved. It highlights the vulnerabilities present in digital systems and the need for comprehensive security protocols. The impact of such leaks can be far-reaching, affecting trust, reputation, and financial stability.
Legal Implications of Leaks
Leak incidents like Lexi 2 Legit often have significant legal ramifications. Laws and regulations governing data protection and privacy are designed to safeguard individuals and organizations from unauthorized access and disclosure of sensitive information. Understanding these legal frameworks is essential for both victims and perpetrators of leaks.
According to a report by the International Association of Privacy Professionals (IAPP), data breach notifications have become a critical component of legal compliance. Organizations are required to adhere to specific guidelines when handling sensitive data, ensuring that any breaches are promptly addressed and reported.
Key Legal Frameworks
- General Data Protection Regulation (GDPR): A European Union regulation that sets standards for data protection and privacy.
- California Consumer Privacy Act (CCPA): A U.S. state law that grants consumers greater control over their personal information.
Ethical Considerations
Beyond the legal aspects, leaks like Lexi 2 Legit raise important ethical questions. The unauthorized release of personal or confidential information can have profound implications for privacy and trust. Ethical considerations emphasize the importance of respecting individual rights and maintaining integrity in digital interactions.
Experts in digital ethics argue that the responsibility lies not only with organizations but also with individuals who use digital platforms. Promoting ethical behavior in the digital space requires a collective effort to prioritize privacy and security.
Best Practices for Ethical Digital Use
- Respect privacy settings and permissions.
- Avoid sharing sensitive information without consent.
- Report suspicious activities or potential breaches.
How to Protect Your Data
Protecting your data in an era of frequent leaks is paramount. Implementing robust security measures can significantly reduce the risk of unauthorized access or disclosure. Below are some practical steps individuals and organizations can take to safeguard their digital assets.
Security Measures
- Use Strong Passwords: Create complex passwords and enable two-factor authentication.
- Regularly Update Software: Keep all systems and applications up to date with the latest security patches.
- Encrypt Sensitive Data: Use encryption tools to protect confidential information.
Famous Data Breaches
History has witnessed numerous high-profile data breaches that have shaped the landscape of digital security. Learning from these incidents can provide valuable insights into preventing future breaches. Below are some notable examples:
Notable Breaches
- Equifax Data Breach: Affected over 147 million consumers in 2017.
- Yahoo Data Breach: Impacted all 3 billion user accounts in 2013.
Impact on Individuals
The impact of leaks like Lexi 2 Legit Leaked on individuals can be profound. Personal information, once leaked, can lead to identity theft, financial fraud, and emotional distress. It is crucial for individuals to remain vigilant and proactive in protecting their digital identities.
Steps to Take After a Leak
- Monitor credit reports for suspicious activity.
- Change passwords and enable additional security features.
- Report the incident to relevant authorities or organizations.
Future of Digital Security
As technology continues to evolve, so too must the approaches to digital security. Innovations in artificial intelligence, blockchain, and cybersecurity are paving the way for more secure digital environments. The future of digital security lies in embracing these advancements while maintaining a focus on ethical and legal considerations.
Emerging Technologies
- Artificial Intelligence (AI): Enhances threat detection and response capabilities.
- Blockchain: Provides secure and transparent data storage solutions.
Conclusion
In conclusion, the phenomenon of Lexi 2 Legit Leaked highlights the ongoing challenges in digital security and the importance of addressing these issues effectively. By understanding the causes, consequences, and solutions related to such leaks, individuals and organizations can better protect themselves in an increasingly digital world.
We encourage readers to take proactive steps in safeguarding their digital presence and to remain informed about the latest developments in digital security. Share your thoughts or experiences in the comments below, and explore other articles on our site for more insights into digital safety and security.