Revolutionizing Connectivity: A Comprehensive Guide to IoT Remote Access
IoT remote access has become a cornerstone of modern technology, enabling users to control devices and systems from virtually anywhere in the world. This transformative capability has redefined how businesses and individuals interact with connected devices, offering unparalleled convenience and efficiency. As the Internet of Things (IoT) continues to expand, understanding the nuances of remote access is essential for leveraging its full potential.
The integration of IoT remote access into daily operations has opened new possibilities across industries, from smart homes to industrial automation. By allowing real-time monitoring and management of connected devices, remote access enhances productivity and reduces operational costs. This article will delve into the intricacies of IoT remote access, exploring its benefits, challenges, and future prospects.
Whether you're a tech enthusiast, a business owner, or an IT professional, this guide will equip you with the knowledge needed to harness the power of IoT remote access. From security considerations to implementation strategies, we'll cover everything you need to know to stay ahead in the rapidly evolving world of IoT.
Introduction to IoT Remote Access
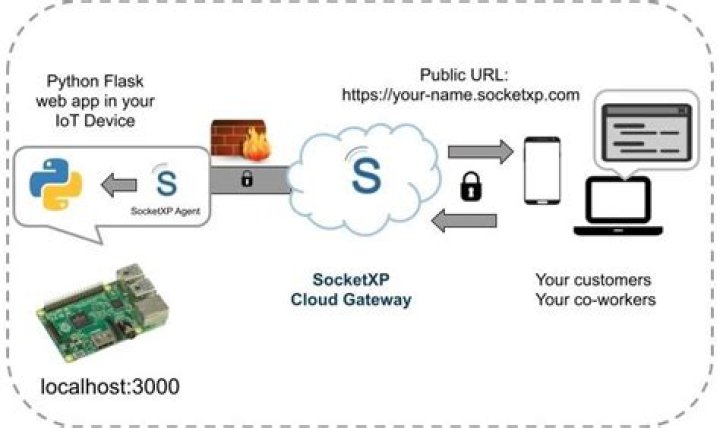
IoT remote access refers to the ability to interact with and manage IoT devices from a remote location. This functionality is achieved through a combination of hardware, software, and communication protocols that facilitate secure and reliable connections. As more devices become connected to the internet, the demand for remote access solutions continues to grow.
Key Components of IoT Remote Access
The foundation of IoT remote access lies in several key components:
- Devices: Smart devices equipped with sensors and actuators that can be controlled remotely.
- Networks: Communication networks such as Wi-Fi, cellular, or LoRa that enable data exchange between devices and users.
- Cloud Platforms: Centralized cloud systems that store and process data from connected devices.
- User Interfaces: Dashboards and applications that provide users with real-time access to device status and control options.
Together, these components create a seamless ecosystem that empowers users to manage their IoT devices with ease and precision.
How IoT Remote Access Works
At its core, IoT remote access operates through a series of interconnected processes that ensure secure and efficient communication between devices and users. This section will explore the technical aspects of how remote access is achieved.
Communication Protocols
Several communication protocols are commonly used in IoT remote access:
- MQTT: A lightweight protocol ideal for low-bandwidth environments.
- CoAP: A protocol designed for constrained devices and networks.
- HTTP/HTTPS: Standard protocols used for web-based interactions.
Each protocol has its strengths and is chosen based on the specific requirements of the IoT application.
Benefits of IoT Remote Access
IoT remote access offers numerous advantages that make it an indispensable tool in today's digital landscape. Some of the key benefits include:
- Increased Efficiency: Users can monitor and control devices without being physically present, saving time and resources.
- Cost Savings: Remote access reduces the need for on-site visits, lowering operational expenses.
- Enhanced Flexibility: Devices can be accessed and managed from anywhere, providing greater convenience and adaptability.
- Real-Time Monitoring: Continuous access to device data allows for proactive decision-making and issue resolution.
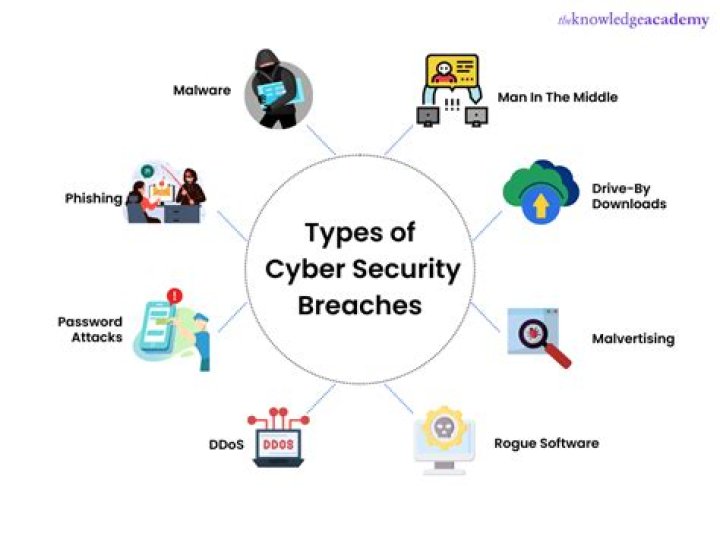
Security Challenges in IoT Remote Access
While IoT remote access provides significant benefits, it also introduces security challenges that must be addressed. These challenges include:
Data Privacy Concerns
With sensitive data being transmitted over networks, ensuring privacy is paramount. Encryption and secure authentication methods are essential to protect user information.
Vulnerability to Cyberattacks
IoT devices are often targeted by cybercriminals seeking to exploit vulnerabilities in remote access systems. Implementing robust security measures is crucial to safeguard against potential threats.
Best Practices for Secure IoT Remote Access
To mitigate security risks, it's important to follow best practices when implementing IoT remote access solutions. Consider the following strategies:
- Use Strong Authentication: Implement multi-factor authentication (MFA) to verify user identities.
- Encrypt Data Transmission: Utilize encryption protocols such as TLS to secure data in transit.
- Regularly Update Firmware: Keep device firmware up to date to address known vulnerabilities.
- Monitor Network Activity: Employ intrusion detection systems to identify and respond to suspicious activity.
Tools and Technologies for IoT Remote Access
A variety of tools and technologies are available to facilitate IoT remote access. Some of the most popular options include:
Remote Management Platforms
Platforms like AWS IoT Core, Microsoft Azure IoT Hub, and Google Cloud IoT Core offer comprehensive solutions for managing IoT devices remotely. These platforms provide features such as device provisioning, data analytics, and rule-based automation.
Mobile Applications
Mobile apps enable users to access and control IoT devices on the go. These apps often include intuitive interfaces and real-time notifications to enhance user experience.
Use Cases of IoT Remote Access
IoT remote access has diverse applications across various industries. Some notable use cases include:
- Smart Homes: Users can control lighting, climate systems, and security cameras from their smartphones.
- Healthcare: Remote monitoring of medical devices allows healthcare providers to track patient health in real time.
- Manufacturing: Industrial IoT enables remote management of machinery and production processes.
- Agriculture: Farmers can monitor soil conditions and irrigation systems remotely to optimize crop yields.
Future of IoT Remote Access
As technology continues to evolve, the future of IoT remote access looks promising. Emerging trends such as 5G networks, edge computing, and artificial intelligence are set to enhance the capabilities of remote access solutions. These advancements will enable faster data transmission, improved processing power, and more intelligent decision-making.
5G and IoT Remote Access
The rollout of 5G networks will significantly boost the performance of IoT remote access systems. With higher bandwidth and lower latency, 5G will facilitate more reliable and responsive connections, paving the way for new applications and use cases.
Common Mistakes to Avoid
When implementing IoT remote access, it's important to avoid common pitfalls that can compromise security and functionality. Some mistakes to watch out for include:
- Ignoring Security Best Practices: Failing to implement proper security measures can leave systems vulnerable to attacks.
- Overlooking Device Compatibility: Ensuring compatibility between devices and platforms is crucial for seamless integration.
- Not Testing Thoroughly: Conducting rigorous testing before deployment helps identify and resolve potential issues.
Conclusion and Next Steps
IoT remote access has revolutionized the way we interact with connected devices, offering unparalleled convenience and efficiency. By understanding its benefits, addressing security challenges, and following best practices, organizations and individuals can fully leverage the potential of IoT remote access.
We encourage readers to explore the tools and technologies discussed in this article and consider how they can be applied to their specific needs. Don't hesitate to leave a comment or share this article with others who may find it valuable. For further insights, check out our other articles on IoT and related topics.